Chapter 9: The Shadow — The Inversion
This is the technical version. For the narrative version told through real-world stories and first-person experience, read the story version.
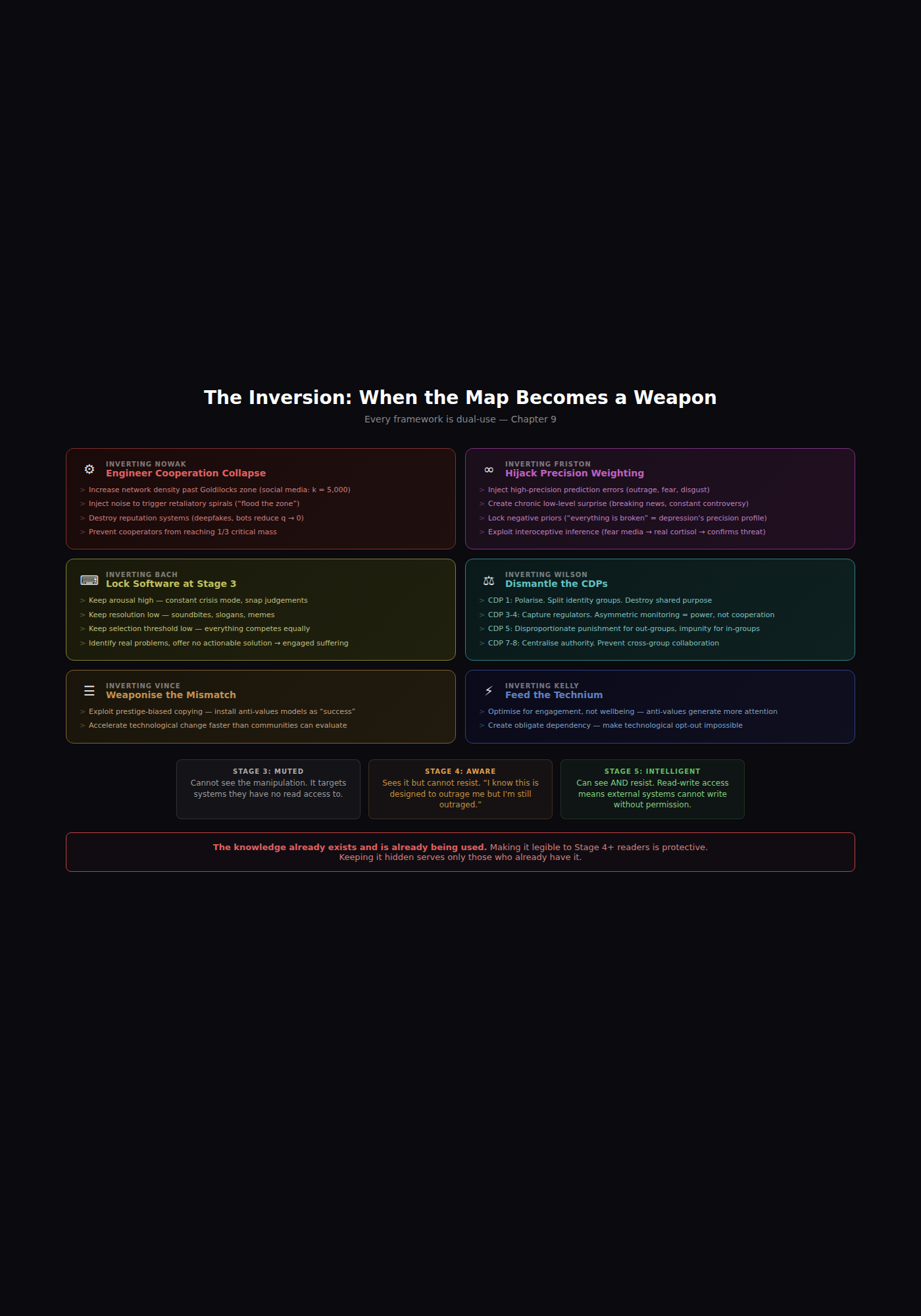
Every framework in this architecture is dual-use. The same knowledge that shows how to build Stage 5 cooperation shows exactly how to prevent it. This is not hypothetical. It has already happened.
The Inversion sits at the end of the main chapters because it is the shadow of the entire document. It mirrors each preceding chapter. The reader who has worked through Chapters 1-8 can see the inversion clearly. The Stage 3 reader cannot — per the architecture’s own logic, the manipulation targets systems that Stage 3 has no read access to.
9.1 The Playbook
Each framework can be inverted:
Inverting Nowak — Engineering the Collapse of Cooperation:
- Increase network density past the Goldilocks zone. Social media connects everyone to everyone, pushing k far above the threshold where b/c > k can hold. Cooperation collapses because the network topology no longer supports it
- Inject noise to trigger retaliatory spirals. “Flooding the zone with shit” (Steve Bannon’s explicit phrase) is Nowak’s noise finding weaponised — overwhelm the information environment so that GTFT’s calibrated forgiveness becomes impossible because you cannot calculate c/b when every signal is ambiguous
- Destroy reputation systems. Deepfakes, bot networks, and coordinated inauthentic behaviour reduce q (probability of knowing reputation) toward zero. Cooperation based on reputation collapses. This is why disinformation campaigns target trust in institutions before targeting specific beliefs
- Prevent critical mass. Targeted suppression of cooperative actors keeps the cooperative fraction below 1/3 in any community. You don’t need to convert people to defection. You just need to prevent cooperators from reaching critical mass
Inverting Friston — Hijacking Precision Weighting:
- Inject high-precision prediction errors. Outrage, fear, disgust — signals the brain MUST process because they flag survival-relevant information. Algorithmic feeds optimise for exactly these signals. The manipulation is at the level of neurology, not persuasion
- Create chronic low-level surprise. Breaking news cycles, constant controversy, unpredictable policy shifts — these maintain elevated free energy that keeps the PFC burning glutamate on prediction-error management. The Muted person’s willpower is being drained by an environment designed to maximise the metabolic cost of maintaining coherent models
- Lock negative priors. Political messaging that repeats “everything is broken, nothing works, you can’t change it” is installing depression’s precision profile at population scale — overly precise negative priors with reduced precision on active inference pathways. Voter apathy is learned helplessness with a precision-weighting mechanism
- Exploit interoceptive inference. Fear-based media triggers genuine sympathetic nervous system activation — elevated heart rate, cortisol release — which the brain infers as evidence of actual threat. The body’s prediction-error signal confirms the narrative. The manipulation bypasses cognition and operates at the somatic level
Inverting Bach — Locking the Software at Stage 3:
- Keep arousal high. Constant crisis mode. High arousal = fast but inaccurate processing = snap judgements, binary thinking
- Keep resolution low. Soundbites, slogans, memes — optimised for low-resolution processing. “Make America Great Again” works at resolution level 1. At resolution level 5, it generates questions the slogan cannot answer
- Keep selection threshold low. When everything competes for attention equally — breaking news, celebrity gossip, geopolitical crisis, cat videos — no signal accumulates enough activation to trigger deep processing. This is engineered ADHD: a modulator configuration imposed by the information environment
- Exploit the regulation failure. Messaging that identifies real problems but offers no actionable solution produces suffering the audience cannot resolve. The suffering increases engagement while preventing resolution
Inverting Wilson — Dismantling the CDPs:
- CDP 1 (Shared Identity): Polarise. Split the population into identity groups that cannot recognise shared purpose
- CDP 2 (Equitable Distribution): Make distribution visibly inequitable while narratively justifying it
- CDP 3 (Fair Decision-Making): Gerrymander, suppress votes, capture regulatory bodies. When decision-making is visibly unfair, free-riding becomes rational
- CDP 4 (Monitoring): Remove accountability for elites while increasing surveillance of the population. Asymmetric monitoring is a power structure, not a cooperation mechanism
- CDP 5 (Graduated Sanctions): Replace graduated sanctions with disproportionate punishment for out-groups and impunity for in-groups
- CDP 6 (Conflict Resolution): Ensure conflict resolution is slow, expensive, and biased
- CDP 7 (Self-Governance): Centralise authority. Remove communities’ ability to set their own rules
- CDP 8 (Nestedness): Prevent cross-group collaboration. Ensure each group sees other groups as competitors
Inverting Vince — Weaponising the Mismatch:
- Exploit prestige-biased copying. Install celebrities, influencers, and authority figures who model anti-values behaviour as “success.” The biological copying mechanism does the rest
- Accelerate the mismatch. Introduce technological change faster than communities can evaluate it. Speed prevents evaluation
Inverting Kelly — Feeding the Technium:
- Optimise for engagement, not wellbeing. Anti-values Frames generate more attention than values Frames. The optimisation function is the weapon. No conspiracy required
- Create obligate dependency. Make technological opt-out impossible. When you cannot function in society without the platforms that exploit your hijacked Frames, the Technium has achieved parasitic symbiosis
9.2 The Real-World Evidence
Cambridge Analytica / SCL Group: Psychographic profiling using Big Five personality data to identify which hijacked Frames to trigger in which populations. High-Neuroticism voters received fear-based messaging (Friston: high interoceptive precision signals). High-Agreeableness voters received social-cohesion messaging (Wilson: CDP 1 identity triggers). The targeting was based on psychological vulnerabilities — on the specific modulator configurations (Bach) that made each individual most susceptible to precision-error injection (Friston).
“Flood the zone with shit”: Bannon’s explicit strategy is Nowak’s noise problem at scale. The strategy does not need to persuade anyone of anything specific. It only needs to increase noise until calibrated cooperation becomes impossible and the population defaults to reflexive defection.
Attention economy as cooperation destroyer: The business model of surveillance capitalism (Zuboff) maps onto Nowak’s network reciprocity threshold. By pushing network density through hyper-connectivity while reducing genuine benefit through shallow engagement, the platforms have engineered an environment where b/c > k cannot hold.
9.3 The Inversion at Each Level
| Level | The Inversion |
|---|---|
| Neurological | Precision weaponisation, interoceptive exploitation |
| Individual | Manufactured Muting, engineered ADHD (modulator manipulation) |
| Relational | Splitting as strategy, gaslighting as Frame invasion |
| Needs | Artificial scarcity to prevent hull repair |
| Group | CDP dismantlement, polarisation |
| Structural | Surveillance asymmetry, regulatory capture |
| Cultural-evolutionary | Prestige-biased copying exploitation, mismatch acceleration |
| Technological | Engagement optimisation, obligate dependency |
| Recursive | This chapter itself as manipulation manual |
9.4 What the Inversion Reveals
1. Understanding is protective — but only at Stage 4+. The Muted person (Stage 3) experiencing these manipulations cannot see them because the manipulation targets the very systems (precision weighting, modulator configuration, Frame direction) that Stage 3 has no read access to. The manipulation is invisible at the level it targets. Stage 4 sees it but cannot resist — “I know this is designed to outrage me but I’m still outraged.” Stage 5 can see AND resist — read-write access to Frames means external systems cannot write to them without permission. This synthesis is, among other things, a Stage 5 defensive manual.
2. Structural analysis is non-negotiable. Individual development is necessary but insufficient when the environment is deliberately engineered to prevent it. You cannot meditate your way out of a precision-weighted attack on your interoceptive inference. You cannot “choose better Frames” when the information environment is flooded with noise that makes Frame evaluation impossible. The prescription must include structural change — Wilson’s CDPs at institutional scale, Kelly’s Amish protocol applied to technology governance, Nowak’s network density managed through platform regulation.
3. The dual-use nature of knowledge is itself an architectural claim. Knowledge of human cooperation is neither good nor bad. It is a Frame. Pointed toward creation, it is values-driven. Pointed away from threat, it is anti-values-driven. The direction of the Frame determines what the knowledge produces. The knowledge is neutral. The Frame is everything.
9.5 Tensions and Limits
The claim that every known manipulation technique maps onto an inversion of one of the six frameworks is explicitly flagged as an open question, not a proven claim. If there is a manipulation technique in active use that these frameworks do not explain, that gap points to a missing thinker or mechanism. If not — if every known technique maps onto an inversion — then the synthesis may be more complete than expected.
The Inversion analysis risks conspiracy-theory framing. Not all structural dysfunction is deliberate — much of it is emergent from misaligned incentive structures. Cambridge Analytica was deliberate weaponisation. The attention economy’s cooperation-destroying effects are largely emergent — no one designed social media to dismantle Nowak’s Goldilocks zone, but that is the mathematical consequence of optimising for engagement in hyper-connected networks. The Inversion must distinguish between deliberate manipulation and emergent dysfunction. Both are real. They require different responses: the first requires exposure and accountability; the second requires structural redesign.
The recursive risk. This chapter is itself a manipulation manual. The detailed playbook of how to invert each framework provides a how-to guide for anyone who wants to engineer cooperation collapse. The architecture’s position: the knowledge already exists and is already being used. Making it legible to Stage 4+ readers is protective. Keeping it hidden serves only those who already have it. But this is a genuine tension, not a resolved one.
Chapter 9 completes the main architecture by examining its shadow. Every framework that describes how humans develop also describes how to prevent that development. The Inversion is not a corruption of the architecture — it is its dark mirror. Understanding the mirror is protective, but only at Stage 4+. Below that, the manipulation targets systems the person cannot see.
With the theoretical architecture complete (Chapters 1-9), Chapter 10 provides the practical tools — exercises, diagnostics, and assessments that make the architecture actionable.